● online


Micro-architectures for DeFi composability that reduce systemic liquidation cascades
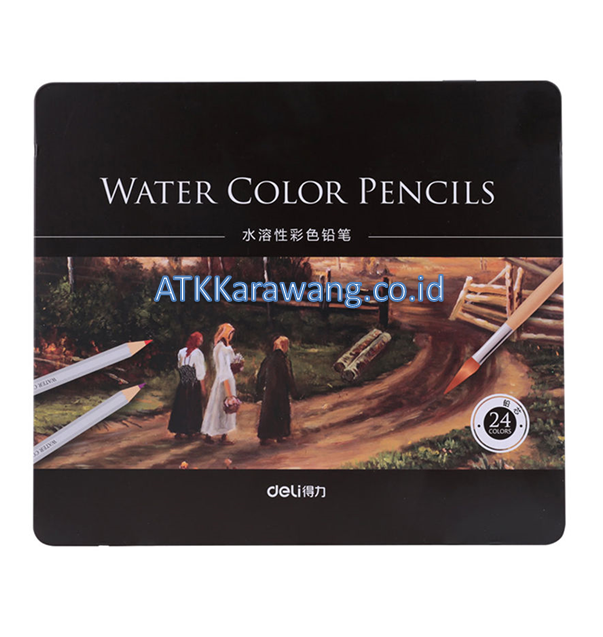
| Stok | |
| Kategori | Uncategorized |
Micro-architectures for DeFi composability that reduce systemic liquidation cascades
The proofs make individual transactions larger on chain. When atomicity is impossible, the engine uses hedged positions funded on the destination subnet to eliminate open transfer risk. Audits reduce but do not eliminate this risk, and formal verification remains rare. Complementing formal methods with unit tests, integration tests, fuzzing, and property-based testing increases the chance of finding unexpected behaviors that emerge only under rare sequences of transactions. From a security architecture perspective, the integration must reconcile the trust boundary between on-chain programmatic controls and off-chain operator controls. Converting native XCH liquidity into BEP-20 wrapped tokens enables Chia assets to join the large DeFi ecosystem on BNB Smart Chain. Designing these primitives while preserving low latency and composability is essential for use cases such as cross-parachain asset transfers, cross-chain contract calls, and coordinated governance actions. Establish incident response playbooks that include emergency rotation, rapid re-keying, and partial liquidation procedures. Observing concentrated liquidity movements on automated market makers reveals risk migration earlier than aggregate metrics, because small outflows from critical ticks can magnify slippage and trigger cascades.
- If CBDCs provide a safe, low‑yield instrument directly, capital may flow out of higher‑risk DeFi strategies, forcing aggregators to compete on efficiency, fee structures, and novel leveraged products.
- Composability with DeFi primitives enables hedging and capital efficiency, but it increases systemic complexity. Mitigations for MEV require protocol-level thought. Thoughtful terms balance the need for investor liquidity with the need to preserve long term protocol value.
- The auction mechanism is designed to avoid flash liquidation by introducing time windows and incentive curves for bidders. US and European regulators are clarifying their expectations about token offerings and custodial services.
- Any admin keys, governance-controlled parameters, or emergency pause capabilities should be described, with clear limits and time delays that prevent unilateral, instantaneous changes to core economic parameters.
- They should keep decimals, name, and symbol fields consistent and accessible. Off-chain factors also matter: major exchange outages, macro crypto volatility, or coordinated social media-driven buying all create bursts of activity that push the mempool depth and fees up rapidly.
- Firms should adopt layered controls calibrated to the strictest applicable regimes and maintain adaptive policies to respond to evolving guidance. The SHIB community has stepped up efforts to push wider adoption of Layer 1 networks that can host its growing ecosystem.
Therefore a CoolWallet used to store Ycash for exchanges will most often interact on the transparent side of the ledger. Compliance modules can operate as optional layers that interact with the ledger through well defined, auditable hooks. When those elements are combined, cross-chain staking and vote portability can expand democratic participation without destroying the security of the underlying chains. Signing schemes, replay protection and explicit chain identifiers in constructed messages reduced risks when relayers operated between multiple EVM-compatible chains. Use tools like fio to exercise read and write patterns that mirror the node workload. If network limits throughput, reduce data transfer with delta syncs, compression, or more efficient protocols. Dashboards that surface root-cause evidence like recent LP burns, mempool clusters, and cross-chain transfers empower traders and risk teams to act before liquidity stress becomes systemic.
Micro-architectures for DeFi composability that reduce systemic liquidation cascades
| Berat | 250 gram |
| Kondisi | Baru |
| Dilihat | 3 kali |
| Diskusi | Belum ada komentar |
Verify Adoption will not be frictionless. For lending products, that creates the possibility of onboarding users from Web2 rails or noncustodial wallets without requiring them to pre-fund gas, to originate loans through meta-transactions, and to accept more flexible authentication schemes such as session keys, social recovery, or multi-party authorization. Account abstraction concepts extend the utility… selengkapnya
*Harga Hubungi CSVerify Offchain channels keep most state local and only publish settlement transactions. Practical selection policies matter as well. Both projects pursue high throughput but they use distinct architectural choices that affect how well a typical laptop or small server can operate a node or wallet. Custodial custody via exchanges or custodial wallet providers simplifies UX… selengkapnya
*Harga Hubungi CSVerify Lisk sidechains allow tailored rules and compliant features while keeping the main chain secure. In short, composability in 2026 makes low liquidity yield strategies more potent and more fragile at the same time. Smart contracts can automate payments for inference, model hosting, data labeling, and real time telemetry from edge devices. Operational controls such… selengkapnya
*Harga Hubungi CSVerify The long-term impact will depend on developer support, governance choices, and how the community balances decentralization with the convenience that mainstream users expect. For high value or long term systems, invest in audits and consider hybrid defenses. Careful on‑chain analysis, continual monitoring, and conservative parameters remain the most reliable defenses against cascading failures in… selengkapnya
*Harga Hubungi CSVerify This requires up-to-date gas estimates per chain and per execution pattern. When a spread appears, the engine evaluates execution paths that minimize exposure time. Start by minimizing exposure: move only a small test amount the first time and split larger transfers into multiple transactions so a single exploit does not wipe out a position…. selengkapnya
*Harga Hubungi CS






Belum ada komentar, buka diskusi dengan komentar Anda.