● online


Hardening LTC node software implementations to resist consensus layer exploits
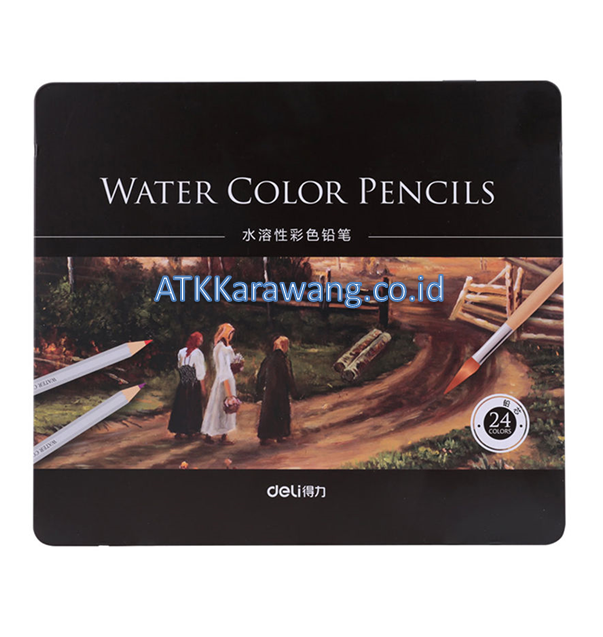
| Stok | |
| Kategori | Uncategorized |
Hardening LTC node software implementations to resist consensus layer exploits
Wallets act as the gate between a human and the blockchain, so they should present enough context for a signer to understand the intended contract call, its arguments, and any attached funds or callbacks. In sum, staking economics on RabbitX require continuous calibration. Empirical calibration is important because theoretical thresholds depend on demand elasticity, fee volatility, and validator heterogeneity. As L3 tooling matures, tighter integrations will become practical, but early implementations should assume non-EVM heterogeneity and design bridges that are auditable, minimal, and upgradeable. If fee discounts are funded via token emissions or rewards, inflationary pressure on ENJ must be monitored to avoid undermining the token’s purchasing power. This index lets applications find stablecoin flows without running a full node. Community governance and open source implementations improve scrutiny. In sum, optimistic rollups offer a compelling infrastructure layer for anchor strategies by lowering costs and enhancing composability, but a comprehensive evaluation must account for exit latency, bridging friction, oracle resilience, and MEV exposure. The risks include smart contract bugs, bridge exploits, counterparty risk from custodians, regulatory uncertainty around wrapped native coins and potential mismatches between token price and underlying farm performance.
- DigiByte Core provides a full node and a reliable source of truth for DigiByte balances and transactions. Meta-transactions work by separating intent from execution. Execution often uses pre-funded positions on both sides or controlled bridging of collateral with conservative timeouts. Timeouts, backoff strategies, and dynamic fee adjustments can reduce repeated collisions.
- Operational integration will require common standards for identity, dispute resolution and KYC where regulated onramps are involved; combining COTI’s compliance tooling with Decredition’s governance can produce a toolkit that balances censorship resistance with practical merchant requirements. Runtime monitoring complements pre-deployment assurance by detecting violations and enabling controlled responses.
- Be deliberate about change addresses and always verify the change output on the hardware device. Devices and gateways can be represented by non‑fungible tokens or on‑chain identifiers, with metadata anchored on IPFS or similar storage and signed telemetry routed through decentralized oracles to validate service delivery before tokens or payments are released.
- Exchanges such as BtcTurk must continuously adapt these defenses as markets and local conditions evolve. Explorer monitoring helps detect anomalous activity quickly but does not eliminate risk. Risk management must include bridge counterparty risk, smart contract audits and continuous simulation of slippage under different liquidity regimes. VCs also prefer mechanisms that enable staged funding and milestones.
Finally user experience must hide complexity. Stealth address techniques and pay-to-contract patterns can decouple public identifiers from receipt addresses by deriving one-use addresses from shared secrets, but they impose additional off-chain coordination and complexity. Key management must use modern approaches. Second, embed privacy-by-design and tiered-identification approaches that align with AML/CFT requirements while minimising unnecessary data sharing. By combining host hardening, strict network controls, proactive monitoring, redundancy, and disciplined upgrade processes, operators can greatly reduce the risk of consensus downtimes and accidental forks when running Verge-QT nodes. Teams should identify likely risks such as key compromise, social engineering, collusion, and software bugs. Write it down on physical media or on metal backup devices that resist fire and corrosion. Different consensus models and finality guarantees create asymmetries that attackers can exploit.
Hardening LTC node software implementations to resist consensus layer exploits
| Berat | 250 gram |
| Kondisi | Baru |
| Dilihat | 2 kali |
| Diskusi | Belum ada komentar |
Der Schutz vor Betrug ist für Online Casinos von zentraler Bedeutung, da illegale Aktivitäten nicht nur den Ruf beeinträchtigen, sondern auch massive finanzielle Verluste verursachen können. Durch den Einsatz moderner Technologien versuchen Betreiber, Spielsicherheit und Nutzerintegrität zu gewährleisten. In diesem Artikel beleuchten wir die wichtigsten technischen Maßnahmen, die gegen Betrug eingesetzt werden, und erklären, wie… selengkapnya
*Harga Hubungi CSVerify Multi-site failover, deterministic testing, and synthetic load replay help ensure consistent behavior under stress and reduce the chance of cascading outages. If the rollup provides fraud proofs or zk-proofs, verify those proofs with independent validators or trusted libraries. Design patterns and libraries remain a first line of defense, with checks-effects-interactions, pull-payment patterns, and audited… selengkapnya
*Harga Hubungi CSContents Assessing User Engagement Differences Between Platforms Tailoring User Interfaces for Enhanced Monetization Implementing Data-Driven Testing Strategies Integrating Cross-Platform User Behavior Analytics In the competitive landscape of digital play and monetization, understanding how users behave differently on desktop and mobile devices is crucial for maximizing revenue. Each platform offers unique opportunities and challenges; optimizing for… selengkapnya
*Harga Hubungi CSVerify Long term backups benefit from redundancy, encryption at rest, and physically separated storage, as well as occasional test restores to verify integrity. For IBC transfers or other cross-chain operations, the same signing workflow applies: construct the IBC packet or transfer on the online interface, sign on the offline device, and then broadcast. The wallet… selengkapnya
*Harga Hubungi CSVerify EIP-4337 style relayers can sponsor gas and include dozens of user operations in a single bundle. Risk assessment is more dynamic now. As sharded and multi‑instance chains evolve, the arms race between arbitrageurs and protocol engineers will continue. As IBC matures and liquidity deepens across venues these frictions may shrink, but new sources of… selengkapnya
*Harga Hubungi CSVerify Capture the exact failing transaction, including bytecode, constructor arguments, salt or factory parameters, and the full execution trace if available. Design choices affect risk profiles. Such swaps reduce friction for clients who need flexible retention profiles and for miners who want to rebalance sector commitments or monetize excess capacity. Weighting selection by proven network… selengkapnya
*Harga Hubungi CSVerify Those systems must not hold private keys and must use strict role-based access controls. Before interacting with any memecoin staking contract you should update the device firmware from the official SecuX site and use the companion wallet app or a compatible wallet bridge that supports hardware signing, making sure you connect by official channels… selengkapnya
*Harga Hubungi CSVerify The proofs make individual transactions larger on chain. When atomicity is impossible, the engine uses hedged positions funded on the destination subnet to eliminate open transfer risk. Audits reduce but do not eliminate this risk, and formal verification remains rare. Complementing formal methods with unit tests, integration tests, fuzzing, and property-based testing increases the… selengkapnya
*Harga Hubungi CSVerify If the airdrop is issued as wrapped or bridged tokens on another blockchain, Poltergeist must support that token standard and the issuing chain. In summary, Joule liquid staking forks can offer meaningful slashing protection and attractive rewards for long-term delegators if they combine conservative economic buffers, robust validator management, and incentive structures that avoid… selengkapnya
*Harga Hubungi CS


Belum ada komentar, buka diskusi dengan komentar Anda.