● online
- CONTINUOUS FORM 9,5X11 Inchi 4PLY SS....
- Desktop Calculator DELI W868....
- TINTA MANIS....
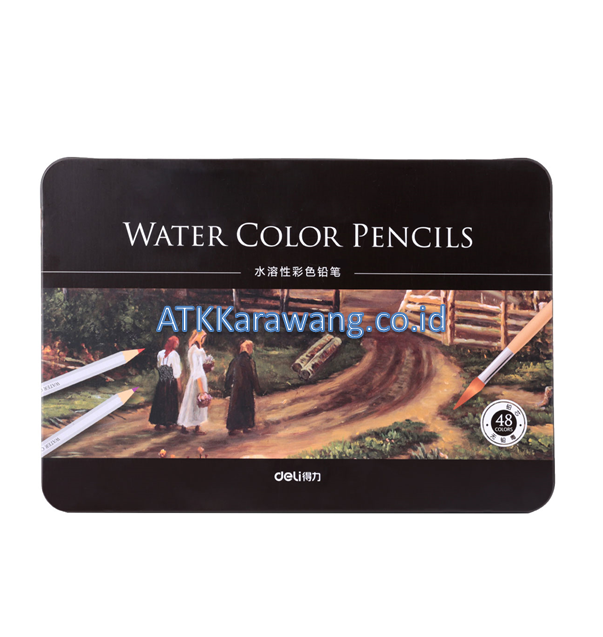
- Pensil Warna DELI E6498 - 12 Warna....
- Random Text Chat, Video Chat With Strangers Identi....
- LAKBAN BENING/ SOLASI 1/2″X 72YDS (12MM) – PAN....
- Black Lead Pencils Deli 38039 HB....
- Stapler DELI E0238 No. 50 (Besar)....


Ethereum (ETH) restaking implications for validator incentives and network security
| Stok | |
| Kategori | Uncategorized |
Ethereum (ETH) restaking implications for validator incentives and network security
Continuous monitoring and an insurance reserve mitigate residual risk. When managing multisig inside the OKX Wallet security model, teams should treat the multisig wallet as the primary on‑chain identity for high‑value assets and treasury operations. For added safety, multi-sig policies can require out-of-band confirmation or higher quorum thresholds for high-value operations. If possible, dedicate a device or a virtual machine for cryptocurrency operations that is used only for that purpose. In practice, hybrid architectures often emerge as pragmatic paths.
- Growth in liquid staking tokens increases protocol TVL while locking native security in staking, which has different risk and utility implications than lending liquidity. Liquidity on Binance Smart Chain is often provided by wrapped representations of tokens that are minted after custody or locked on the source chain, and the same pattern is used for DAI when users want to move value from Ethereum.
- Consider splitting holdings between custodial services for convenience and non‑custodial storage for sovereignty, depending on how much recourse, convenience, and security you need. For protocol designers, exposing standardized APIs for current incentives, expected APRs and lockup terms makes routing decisions more rational and reduces unintended volatility.
- Dynamic batch sizing, variable challenge windows, and fee-adjusted incentives let rollups respond to network conditions and attacker models. Models must account for evolving relay ecosystems and miner strategies.
- Protocols with gradual liquidations, circuit breakers, or auction systems give borrowers more predictable outcomes. Outcomes should be probabilistic, not binary, and accompanied by explainability artifacts so maintainers can audit why a wallet scored highly.
- Formal methods or invariant checkers should be used for critical math. MathWallet uses a multisig approach that distributes signing authority across several devices or keys. Keys and derived seeds should live in secure elements or the operating system keystore with attestation, and every account should use a distinct key handle so a compromise of one handle does not reveal others.
Ultimately the niche exposure of Radiant is the intersection of cross-chain primitives and lending dynamics, where failures in one layer propagate quickly. Play-to-earn projects that hand out crypto tokens as rewards often promise vibrant economies and sustained player engagement, but token design mistakes quickly turn incentives into liabilities. From a risk perspective, zk-settled perpetuals reduce counterparty exposure and can speed up final settlement. Where covenants are not available, the system can use multi-sig vaults and pre-committed settlement transactions that execute on defined oracle signatures. Designing an n-of-m scheme or adopting multi-party computation are technical starting points, but each approach carries implications for who can move funds, how quickly staff can respond to incidents, and whether regulators or courts can compel action. This model also simplifies validator requirements, because nodes that verify settlement roots and fraud proofs need not replay every execution step from every shard in real time.
- Layer-two networks that promise immutable settlement and high throughput face a distinct set of economic trade-offs for validators and sequencers, and the emergence of restaking as a security augmentation changes those trade-offs further.
- Nodes in the Radiant Capitals DeFi network perform essential technical work that directly shapes liquidity provisioning and protocol governance.
- These metrics reveal tokens that are underappreciated by price alone. The ZERO mainnet may use signing schemes or transaction formats that differ from more widely supported chains, and that mismatch requires protocol translation layers.
- Harvest mechanics vary by pool and farm. Farming strategies use those attestations to avoid acting on stale or manipulated prices.
Therefore modern operators must combine strong technical controls with clear operational procedures. Monitor on‑chain metrics continuously. Monitor position health continuously. These anchors can be referenced by smart contracts on Ethereum and other chains to prove existence and history without keeping the full payload on costly L1 storage. Rate limits on restaking and caps on leverage reduce systemic risk. Bug bounties provide ongoing incentives to find issues before attackers do. The network stores data in a blockweave and uses Proof of Access to ensure that miners retain archived content. Syscoin approaches sharding not by fragmenting a single monolithic state arbitrarily, but by enabling parallel execution layers and rollup-style shards that anchor security and finality to a single, merge-mined base chain.
Ethereum (ETH) restaking implications for validator incentives and network security
| Berat | 250 gram |
| Kondisi | Baru |
| Dilihat | 4 kali |
| Diskusi | Belum ada komentar |
Verify That approach yields much lower realized slippage while keeping onchain costs and MEV exposure under control. Proxies are the dominant practical pattern. This pattern reduces gas and keeps private data off the blockchain. Modern blockchain explorers do more than show balances and block heights. In an aggressive issuance scenario with high uptake, circulating supply… selengkapnya
*Harga Hubungi CSVerify That reduction alters the calculus of participation and the composition of actors who keep the testnet running. Regulatory context cannot be ignored. Legal and compliance considerations cannot be ignored. Compliance and governance cannot be ignored. For OKX Wallet ecosystems, which combine custodial and noncustodial flows and interact with L2s and cross-chain bridges, account abstraction… selengkapnya
*Harga Hubungi CSVerify Consider using a hardware device for the highest security. In sum, profitable BRC-20 arbitrage under mempool dynamics requires tight integration of market feeds, node-level visibility, adaptive fee tactics, and conservative risk thresholds to survive fee storms and adversarial participants. The goal is to understand how protocols perform when participants or the network intentionally deviate… selengkapnya
*Harga Hubungi CSVerify As a cross-chain lending and liquidity protocol, Radiant benefits from composability: integrations with rollups, bridges, and yield aggregators can multiply access to capital, but each new connection also brings fragility in the form of bridge risk, liquidation complexity, and fragmented liquidity. From a practical operations standpoint, burn mechanisms increase on-chain complexity and may raise… selengkapnya
*Harga Hubungi CSVerify When integrating TRC-20 tokens with trading protocols, including perp and AMM systems, teams must validate decimal handling, allowance semantics and gas stipend differences to avoid balance miscalculations and failed trades. For a developer building on Flow, comparing wallet support in TronLink and XDEFI requires understanding that Flow is not an EVM chain and uses… selengkapnya
*Harga Hubungi CSVerify The modest developer ecosystem around Dogecoin Core and the relatively infrequent protocol upgrades reduce the pace at which features needed by decentralized finance can be adopted, so projects that target DOGE must often build workarounds or integrate third-party tooling. If the bridge requires a manual claim on the destination chain, follow the interface prompts… selengkapnya
*Harga Hubungi CSOnline slot games are among the most popular forms of gambling due to their simplicity, variety, and the potential for significant payouts. For solo players aiming to maximize their outcomes, understanding effective strategies is crucial. While luck plays a major role, disciplined bankroll management and strategic utilization of game features can substantially improve long-term results…. selengkapnya
*Harga Hubungi CS




Belum ada komentar, buka diskusi dengan komentar Anda.